As the Internet of Things (IoT) expands, managing and monitoring devices behind firewalls has become essential for ensuring security and efficiency. Firewalls are crucial components in safeguarding networks and IoT devices from unauthorised access and cyberattacks. They control incoming and outgoing network traffic. Using predefined rules to maintain security and prevent data breaches. However, the biggest challenge is to monitor IoT behind firewall, and it’s crucial to employ effective strategies.
In this article, we’ll explore the best practices to monitor IoT behind firewalls. Focusing on techniques like port forwarding, VPNs, and SSH. You’ll learn how to employ security in your IoT workloads and utilise remote access solutions to ensure a safe and efficient IoT environment. Understanding the importance of and mastering remote monitoring will enhance the security and performance of your IoT network.
Understanding IoT and Firewall

The Internet of Things (IoT) is the network of corresponding physical devices, vehicles, buildings, and more. They are entrenched with sensors and software to enable communication and data exchange. IoT devices have become crucial in our daily lives, as well as in industrial and enterprise environments. Well, implementing proper safety measures and practices through them, such as zero trust security. Furthermore, it enhances IoT infrastructure protection, ensuring that devices and networks remain uncompromised.
Monitor IoT Behind Firewall: Why?
- Visibility and Control: The firewall should provide you with a clear understanding of which devices are connected, their communication patterns, and the ability to enforce policies for each device.
- Threat Prevention: The firewall should support advanced security features such as intrusion prevention, antivirus protection, and application control to safeguard your IoT devices from threats.
- Scalability: As your IoT deployment grows, your firewall should be able to scale with it, ensuring consistent security for all devices.
- Integration: The IoT firewall should integrate easily with your existing network infrastructure and other security solutions for seamless functionality.
4 Ways To Monitor IoT Behind Firewall Effectively

Every Monitor IoT Behind Firewall aims to provide secure, remote access to devices connected to the internet. Hence, by understanding these aspects of IoT firewalls, you can make better decisions about protecting your IoT devices and networks from cyber threats.
1. Security Checks
Securing IoT devices and networks is paramount to protect sensitive data and ensure smooth functioning. IoT devices may be vulnerable to unauthorised access and cyber threats. It’s essential to protect them behind a firewall.
A firewall is a security system that prevents unauthorised access to your IoT devices. Helps to inspect traffic and allow only authorised traffic to pass through. This way, it is possible to monitor and manage IoT devices safely and securely. If you want to share anything in real time, then sharing through ms team screen share can help you.
2. Monitoring and Management
To effectively monitor IoT behind Firewall and manage your IoT devices behind a firewall, you should ensure that all traffic is captured and logged by the firewall. This enables the IoT Security system to coordinate data received from all firewalls at the same site and monitor devices across the network.
Proper configuration of IoT devices and firewalls allows administrators to maintain visibility and control of IoT security while protecting the devices from cyber threats. Additionally, cloud-based solutions enable seamless monitoring by offering a secure way to communicate with your devices.
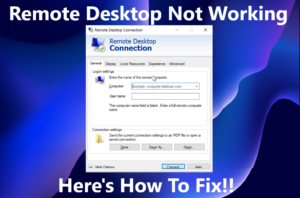
3. Remote Access and Control
Remote access and control of IoT devices behind a firewall is crucial for managing IoT networks and ensuring smooth operation. For instance, in an innovative home environment, you may need to access the settings of various appliances even when you’re not physically present. Well, you can check our guide about remote control for iPads.
Ensuring secure remote access through appropriate authentication and encryption methods is vital to maintain security. At the same time, allowing authorised users the required level of control over their IoT devices. You can also use solutions like Azure IoT Hub to streamline device connectivity monitoring.
4. Communication and Data Transfer
For IoT devices to work effectively, they need to communicate and transfer data among themselves. The use of standard protocols and secure communication channels ensures smooth data transfer and prevents unauthorised access. As a user, consider choosing devices that support widely used communication standards to ensure streamlined communication among your IoT devices.
How to Access IoT Devices Behind a Firewall?

Securing IoT devices with firewalls involves implementing several best practices. First, segment your IoT network by placing devices on dedicated subnets, reducing exposure to other devices and networks. Apply a zero-trust security model, ensuring that every connection request is authenticated before access is granted.
- Port Forwarding: Configuring port forwarding on your router directs incoming traffic from specific ports to targeted IoT devices in your network. This helps you access your devices remotely while maintaining security. However, ensure you only open necessary ports. Well, exposing too many can lead to potential security risks.
- Virtual Private Network (VPN) Set Up: A VPN creates a secure tunnel between your device and the IoT devices. By connecting to a VPN server located within your local network, you can remotely monitor IoT behind firewall. VPNs not only provide remote access but also encrypt your data.
- Secure Shell Protocol (SSH): SSH provides secure remote access to IoT devices by creating an encrypted connection. It lets you perform command-line operations and securely transfer files to your devices. Also, ensuring data privacy and protection from unauthorised access.
Troubleshooting IoT Behind Firewall
Since IoT devices are subject to various external influences, it is possible that they might encounter issues and require troubleshooting. Diagnosing and resolving issues behind a firewall can be complex. Making it essential to have a comprehensive understanding of both the IoT devices and the firewall’s configurations. Regular monitoring, log analysis, and real-time alerts can play a significant role in detecting. Resolving these issues are crucial before they escalate into serious security concerns or operational disruptions.
Frequently Asked Questions
Q1. How can I set up firewall rules for IoT devices?
Start identifying the necessary ports and protocols your devices use to communicate. Once you’ve mapped out your network, create access-control rules to permit only authorised traffic. Ensure that inbound connections are limited to only necessary ports and trusted sources. Regularly review and update your firewall rules to maintain security within your IoT network.
Q2. How does a cellular firewall protect IoT?
A cellular firewall protects IoT devices by filtering incoming and outgoing traffic over cellular networks. It restricts access to necessary ports and trusted sources and ensures compliance with specific mobile networks. Additionally, cellular firewalls track data usage, enabling you to monitor the activity of your IoT devices.
Q3. What methods can monitor activity on IoT devices behind firewalls?
Monitoring activity on IoT devices behind firewalls can be implemented using various techniques.
- Intrusion detection systems (IDS) and
- intrusion prevention systems (IPS) c
- Advanced Threat Protection (ATP)
- Security Information and Event Management (SIEM)
Q4. Why is a firewall crucial for IoT security?
A firewall is crucial for IoT security because it is the first line of defence against unauthorised access and cyber threats. Firewalls help enforce strict access control, permitting only authorised traffic while blocking potential attacks. They also contribute to an organisation’s ability to maintain compliance with regulations and security requirements.
Q5. What are the key aspects of IoT security monitoring?
The key aspects of IoT security monitoring include continuous visibility, threat detection, and appropriate response. To achieve this, you should regularly monitor your IoT network traffic, review firewall logs, and use IDS/IPS to detect suspicious activity.
Conclusion
To sum up, monitoring IoT devices behind a firewall is a crucial aspect of IoT security and management. By understanding the importance of IoT and firewalls, you can implement appropriate security measures, monitor IoT behind firewall effectively, and maintain control over your IoT ecosystem. Various methods for accessing IoT devices behind firewalls include port forwarding, Virtual Private Networks (VPNs), and Secure Shell (SSH) protocols.